Telecoms, ICT & Digital Finance Auditors & Finance
TECHNICAL AUDIT FINANCIAL AUDIT I/T AUDIT COMPLIANCE VERIFICATIONREVENUE ASSURANCE AUDIT
The GRAPA Telecoms Audit Certification equips modern financial auditors with the latest best practices for auditing in cutting-edge telecom and digital finance environments, including 5G, Digital Finance, Fiber, MPLS, and more. This certification provides professionals, as well as their managers and stakeholders, with the confidence that they understand their role, how to perform audits professionally, and how to add strategic value to the financial and operational integrity of their organizations.
Telecoms auditors certified by GRAPA have mastered a broad and deep spectrum of audit methodologies and risk assessment techniques. They understand the diverse challenges related to financial controls, regulatory compliance, fraud detection, and operational assurance in rapidly evolving telecom and digital finance landscapes. Their expertise ensures they can minimize financial risk, enhance profitability, and strengthen compliance, while optimizing outcomes for their organization.
When it comes to Telecoms Audit there is always more to learn. But having someone provide focus on the most important areas to make that process as quick and easy as possible is one of the major benefits our programs offer.
Our approach allows the professional to mix and match the different classes in order to get exactly those areas they need to focus on.
Insert raw html here.
Here is an example of hyper link JoomShaper

4 Designated Certification Tracks to Choose From
A GRAPA Designated Certification Track is a structured and officially recognized sequence of courses designed to guide professionals toward certification. These tracks are curated by industry experts to ensure alignment with global standards and best practices. They include core courses necessary for foundational knowledge and electives that allow some customization based on individual or organizational needs. The objective is to provide a clear, goal-oriented path to achieving certification efficiently and effectively.
Program crafted to equip professionals working with 2G, 3G, 4G, or 5G carriers. This track provides comprehensive background knowledge and exposure to the critical areas necessary for the successful detection, in-depth investigation, root cause analysis, and resolution of revenue and margin leakage across all dimensions of a GSM/Mobile carrier’s operations.
Tools & strategies necessary to optimize operational efficiency & address leakage risks across fixed-line and broadband service ecosystems.Critical technical, operational, and financial best practices.
Purposefully designed to empower professionals navigating the highly dynamic and often chaotic world of Corporate Services, MPLS, Cloud, and Wholesale lines
of business.
How RA fits into ICT. Different disciplines, risks and tools applied to voice, data, fiber, kubenetes, cloud, finance and the rest.
Standards for the professional practice of RA in ICT. Principles, ethics, best practices and methodologies and how they are applied.
An overview of the diverse application of controls to different ICT Lines of Business.
Explores fraud management frameworks, GRAPA standards, and methodologies like FISHbone, Incident Management Lifecycle, and more. Discusses the uniqueness of Telecom fraud management compared to other industries.
How to audit voice traffic networks
How IA protects voice traffic at the network level. Leakage starts at the network level. Assuring CDRs, Network Elements and Provisioning.
Best practices in the auditing of voice traffic. Prepaid, postpaid and convergent billing controls and issues.
Best practices in the auditing of Data traffic. How to be sure that all of the data is accounted for, and standard controls.
Auditing of Next generation prepaid and radius billing for 3G and 4G traffic. Securing GPRS traffic and understanding how 3G and 4G data are managed.
Auditing Local & Global Interconnect (Intercarrier Traffic)
Governance and audit of local and international interconnect partnerships. Partner lifecycle audit issues and controls for voice.
Partner audits, TAP File, DCH and roaming partnership issues, controls and leakage best practices.
Best practices in the audit of Fixed Networks. Cable, Fiber, DSL.
Governance of corporate services, commercial grade broadband, MPLS, leased lines, corporate clouds, corporate private networks, managed services, cloud services.
Assuring Closings, Recognition & Reports
Revenue recognition controls and assurance. Assurance and support for closings. Accounting process controls.
Protecting the revenues and profits of MVNO, MVNE , MNO and all variations of Virtual Carrier. Deep controls, boundary controls and the special issues critical to MVNO operations.
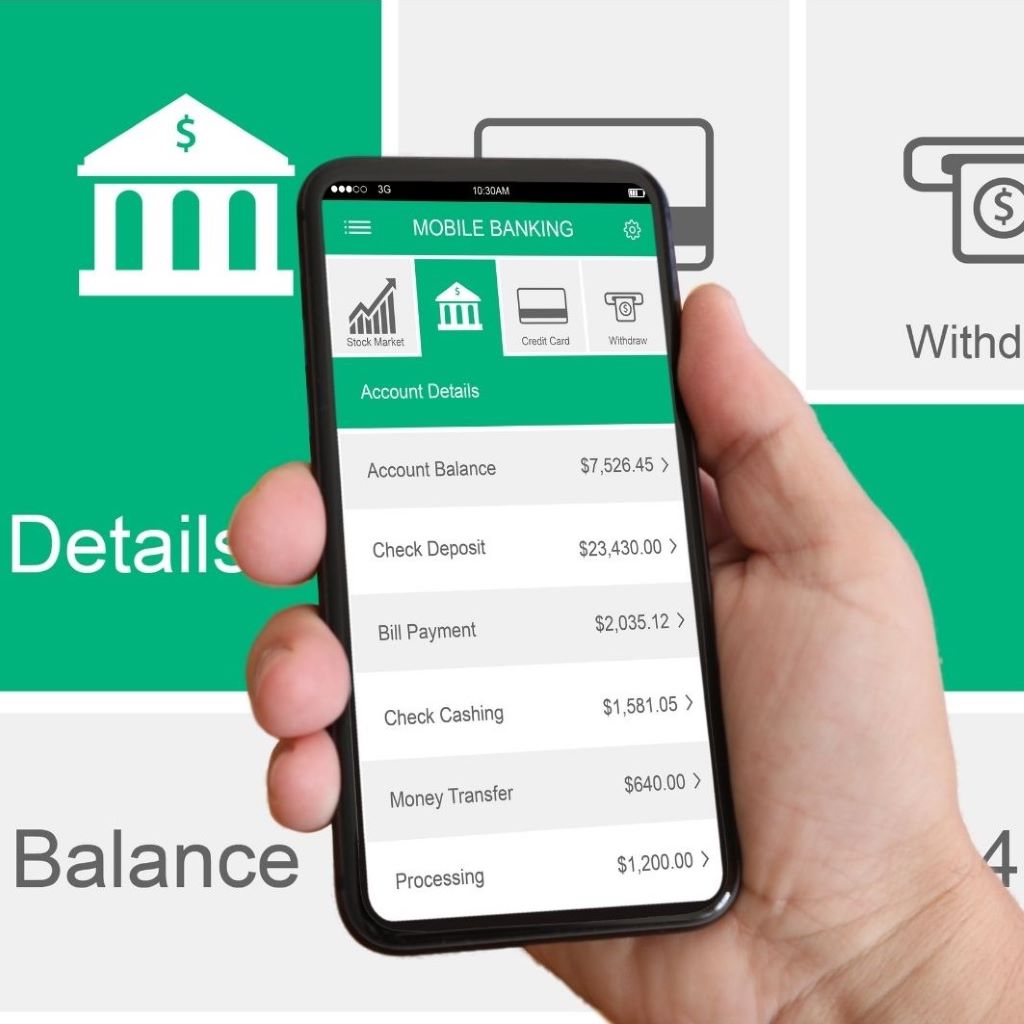
Assuring digital finance revenues for mBanking, agents, banks, partners and electronic funds transfer. Understanding CCSA and PCI DSS.
Controls for VSAT, Ground Stations, Satellite Frenquency and security. Protecting broadcast , signal encryption and security.
This course provides the student with a comprehensive review of the different ways that hackers and cyber criminals physcially breech the radio, fiber and cable connections of the service providers. Key background for anyone in Fraud.
This course provides the student with a comprehensive review of the different ways that hackers and cyber criminals use programming techniques to make hacks and fraud happen.
Social Engineering - the science of hacking people. How do fraudsters trick people into doing things they usually would not. Social engineering is not a trick, it is a science, a skilled application of psychological and neurological principles.